SOC-as-a-Service
Enterprise-grade security monitoring, AI-powered threat detection, and rapid incident response delivered around the clock by Cyber Citadel's expert analysts.
Your Security Operations Centre, Fully Managed
Aegis is Cyber Citadel's fully managed Security Operations Centre delivered as a service. Our team of experienced cyber security analysts monitors your environment continuously, combining advanced detection technology with expert human analysis to identify and respond to threats that automated tools alone will miss.
From network and endpoint monitoring to cloud workload protection and user behaviour analytics, Aegis covers your entire attack surface. You get the security capabilities of a world-class SOC with predictable monthly pricing and no infrastructure to build or maintain.
Continuous coverage by experienced SOC analysts every hour of every day
Behavioural analytics, machine learning, and custom correlation rules
Containment and remediation within minutes of confirmed threats
Analysts actively search for hidden threats beyond automated alerts
Live feeds from worldwide sources integrated into detection rules
Everything You Need in a Security Operations Centre
Aegis delivers a complete suite of SOC capabilities, each backed by experienced analysts and purpose-built technology.
Continuous Security Monitoring
Round-the-clock monitoring of your network, endpoints, servers, cloud workloads, and applications. Our analysts correlate events across your entire infrastructure to detect threats in real time.
Advanced Threat Detection
Multi-layered detection combining signature analysis, behavioural analytics, machine learning models, and custom correlation rules tuned specifically for your environment and industry.
Incident Response and Containment
When a threat is confirmed, our team acts immediately to contain the incident, minimise damage, and begin remediation. You receive clear communication at every step from detection through resolution.
Proactive Threat Hunting
Our analysts do not wait for alerts. They actively search your environment for indicators of compromise, attacker footholds, and latent threats that may have evaded automated detection systems.
SIEM Deployment and Management
Full lifecycle management of your Security Information and Event Management platform, including deployment, configuration, rule tuning, content development, and ongoing performance optimisation.
Log Collection and Correlation
Centralised log ingestion, normalisation, and expert analysis across your entire infrastructure. We correlate events from firewalls, endpoints, identity systems, cloud platforms, and applications.
Threat Intelligence Integration
Real-time threat intelligence feeds from global sources integrated into our detection rules. Our analysts contextualise alerts with the latest intelligence on active campaigns and threat actors.
Compliance and Regulatory Reporting
Comprehensive reporting aligned with GDPR, PCI DSS, HIPAA, ISO 27001, Essential Eight, NIST CSF, and other frameworks. Our reports simplify audits and demonstrate your security posture.
Vulnerability Management
Continuous vulnerability scanning and assessment integrated into the SOC workflow. Discovered vulnerabilities are prioritised by risk and fed directly into remediation tracking.
Security Posture Reviews
Regular assessments of your overall security posture, including configuration reviews, policy audits, and gap analysis against industry best practices and frameworks.
Red Teaming and Penetration Testing
Included in every Aegis engagement. Our offensive security team tests your defences through simulated attacks, ensuring your security controls work when it matters most.
Executive Reporting and Briefings
Board-ready reports and regular executive briefings that translate technical security data into business risk language. Keep leadership informed without overwhelming them with technical detail.
Aegis AI: Smarter, Faster, Always Learning
Aegis combines the judgement of our human analysts with the speed and scale of artificial intelligence. Our AI capabilities augment every stage of the security operations lifecycle, from initial alert triage through to post-incident analysis, enabling faster detection, smarter prioritisation, and more efficient response across your entire environment.
Built for Performance
Every hour. Every day. No gaps in coverage.
From alert to analyst investigation in under 15 minutes.
Guaranteed availability backed by our service level agreement.
Billions of events processed, correlated, and analysed every day.
AI-driven triage eliminates noise so analysts focus on real threats.
GDPR, PCI DSS, HIPAA, ISO 27001, NIST, Essential Eight, and more.
From Onboarding to Full Protection
We make the transition seamless. Our structured onboarding ensures you are fully protected from day one with minimal disruption to your operations.
Discovery and Scoping
We assess your environment, identify critical assets, map your attack surface, and understand your risk profile to tailor the service to your specific needs.
Integration and Deployment
We deploy sensors, configure log sources, integrate with your existing security tools, and establish secure connectivity between your environment and the Aegis platform.
Baseline and Tuning
Our analysts establish behavioural baselines for your environment, tune detection rules to reduce noise, and develop custom correlation content for your specific threat landscape.
Continuous Operations
24/7 monitoring, threat hunting, incident response, regular reporting, and ongoing optimisation. Your security posture is continuously strengthened and adapted to evolving threats.
More Than Just Monitoring
Most managed SOC providers stop at monitoring and alerting. Aegis goes further by including proactive security services that no other SOC provider offers as standard. Your security posture is not just watched; it is actively tested and strengthened on an ongoing basis.
Aegis clients also benefit from direct access to Cyber Citadel's full range of offensive security services, including penetration testing, source code review, and digital forensics. This integrated approach means the same team that detects a vulnerability can help you remediate it.
Regular assessments of your configuration, policies, and controls against industry best practices
Simulated attacks by our offensive security team to validate your defences under real-world conditions
Continuous scanning and prioritised remediation guidance integrated into the SOC workflow
Auto-generated SOC reports, live dashboards, and AI security assistant via our Citadel53 platform
What Lies Beneath: SOC-as-a-Service
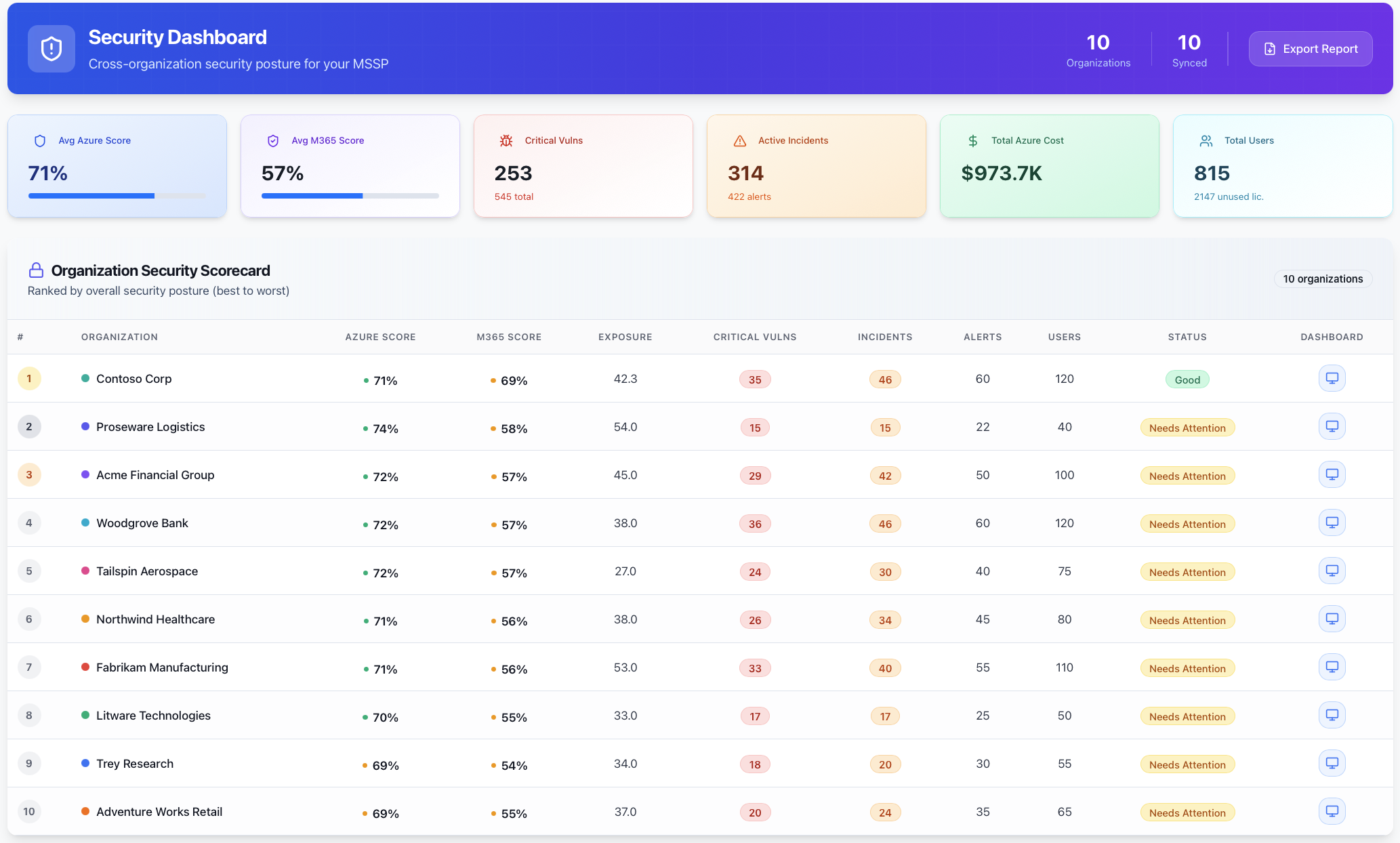
Auto SOC Reports with Citadel53 Security Portal
Citadel53 integrates directly with your Aegis SOC-as-a-Service to automatically generate comprehensive SOC reports with no manual effort required. Reports include threat intelligence summaries, incident analysis, exposure management findings, and security posture assessments.
Beyond SOC reports, Citadel53 provides real-time visibility into your security posture with interactive dashboards for Azure Secure Score, incidents, device compliance, vulnerabilities, and Essential Eight compliance, all from a single unified platform.
- ✓Automated SOC reports with one-click PDF generation
- ✓Real-time incident and security posture dashboards
- ✓Executive reports for board and leadership
- ✓Essential Eight compliance audit and export
- ✓AI-powered security assistant for posture queries
- ✓Azure cost analysis and optimisation recommendations
Who Is Aegis For?
Growing Organisations
Companies that need enterprise-grade security but do not yet have the scale to justify building an in-house SOC.
Regulated Industries
Healthcare, finance, logistics, and government organisations with strict compliance and reporting requirements.
Cloud-First Businesses
Organisations running on Azure, AWS, or GCP that need specialised cloud security monitoring and threat detection.
Lean IT Teams
Businesses with small IT teams that cannot staff a dedicated security operations function around the clock.
Critical Infrastructure
Energy, utilities, and transport operators requiring continuous monitoring of both IT and OT environments.
Frequently Asked Questions
SOC-as-a-Service is a fully managed Security Operations Centre delivered on a subscription basis. Instead of building and staffing your own SOC, Cyber Citadel's Aegis platform provides 24/7 security monitoring, threat detection, incident response, and compliance reporting as a managed service.
Aegis monitors your entire attack surface including network infrastructure, endpoints, servers, cloud workloads (Azure, AWS, GCP), applications, email systems, identity platforms, and IoT/OT environments. We integrate with your existing security tools and collect logs from all critical sources.
Our mean time to respond is under 15 minutes. When a potential threat is detected, our analysts immediately investigate, validate, and take containment action. You receive clear communication throughout the process, from initial detection to full resolution.
Aegis uses artificial intelligence for alert triage, behavioural analytics, and automated playbook execution. Our AI engine reduces false positives by over 90%, allowing analysts to focus on genuine threats. Machine learning models continuously adapt to your environment, improving detection accuracy over time.
Aegis provides reporting aligned with GDPR, PCI DSS, HIPAA, ISO 27001, NIST Cybersecurity Framework, Essential Eight, SOC 2, and other major regulatory frameworks. Reports are designed for auditors, regulators, board members, and executive leadership.
Yes. Every Aegis engagement includes security posture reviews, vulnerability assessments, and red teaming as standard. No other managed SOC provider includes these proactive offensive security services in their offering.
Citadel53 is our security management portal that integrates directly with Aegis to provide automated SOC reports, real-time dashboards, Essential Eight compliance audits, Azure cost analysis, and an AI-powered security assistant, all accessible from a single unified platform.
Typical onboarding takes two to four weeks depending on the complexity of your environment. This includes discovery, integration, baseline tuning, and custom detection content development. You are fully protected from day one with monitoring active during the tuning period.
